Here’s an excerpt from a recent Security Now episode. The TL;DR is that some one can get your PGP decryption key from your computer with an AM radio and a phone nearby.
STEVE: Yeah. So, okay. This generated more tweets this last week than anything else. And I have to say that it was the pita bread that really put the icing on the cake. The fact that you could tuck this thing into a piece of pita bread, that - I don’t know. I was going to call it a “tempest in a teapot,” because of course Tempest is the famous technology for using radiation from something for spying, so “tempest in a Teapot.” But I thought, well, no, “Tempest in a Pita Bread” doesn’t quite have the same ring. So this is an early look at a paper that will be presented at the Workshop on Cryptographic Hardware and Embedded Systems this coming September 2015.
Some beautiful engineering on the part of these researchers. And quoting from their page, they said: “We successfully extracted encryption keys from laptops of various models running GnuPG - popular open source encryption software implementing the OpenPGP standard - within a few seconds. The attack sends a few carefully crafted ciphertexts.” This is the brilliant part. “The attack sends a few carefully crafted ciphertexts, and when these are decrypted by the target computer, they trigger the occurrence of specially structured values inside the decryption software. These special values cause externally observable fluctuations in the electromagnetic field surrounding the laptop, in a way that depends upon the pattern of key bits - specifically, the key bits window in the exponentiation routine. The secret key can be deduced from these fluctuations, through signal processing and cryptanalysis.”
PADRE: Wow.
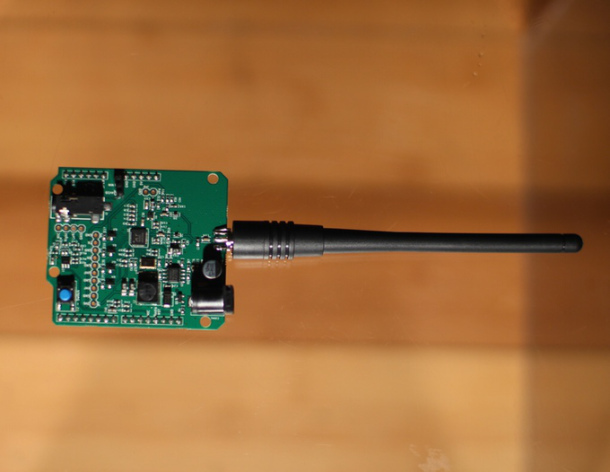
STEVE: It’s just a beautiful piece of work. So, oh, and so they have multiple versions of this. In their first one, they use an SDR, a software-defined radio, and a wire going off to about a six-inch diameter loop, which they hold near the laptop. It can work a few feet away, but it still needs relative proximity. And of course if they improve, if they invested time in directionality and signal amplification, they could end up with a gun sort of thing that you point at a laptop. But, I mean, it isn’t the case that the key bits are just tumbling out.
The secret to their cleverness is that they exactly understood the open source algorithm. They were able to determine that, by causing it to decrypt a specific ciphertext, the act of decrypting it would generate relatively low-frequency transience. That’s the other thing, is even though the processor is cranking away at 3GB, the actual signal that comes out is about in the 1.7 MHz range, way lower.
And in fact, I said that that first attack used a USB SDR connected to a big loop. Then they came up with a battery-powered one - that’s where the pita bread comes in - because they demonstrate, in fact, that’s the picture of the week on the show notes this week is their loop with a power supply, four AA batteries, the SDR, and a small battery-powered computer to drive it and collect the signal, all sitting on top of a piece of pita bread, which you imagine you might be able to slice open and just tuck it in there. And if you just sort of - if there was a lumpy-looking pita bread sitting next to your laptop at Starbucks, you might want to think twice about using PGP to decrypt incoming mail that you weren’t expecting because that could contain the special ciphertext and leak your PGP keys to the pita bread which is nearby.
PADRE: If you’re in the office, and one of your coworkers is walking around with a gyro all day, then, no, maybe you want to take a look at it, just a little.
STEVE: Well, and I loved - their final refinement of this was the so-called “consumer radio attack,” which is the last picture there on the page, showing an AM radio with its earphone jack plugged into a standard smartphone. They said of the consumer radio attack: “Despite its low price and compact size, assembly of the pita device still requires the purchase of an SDR device. As discussed, the leakage signal is modulated around a carrier of around 1.7 MHz, located in the range of the commercial AM radio frequency band. We managed to use a plain consumer” - I don’t even know where they found a plain consumer-grade radio receiver. You know, it look like something with a nine-volt, well, it’s called a transistor radio battery for that reason, you know, that we listened to in the '70s. But so they used “a plain consumer radio to acquire the desired signal, replacing the magnetic probe and the SDR receiver. We then recorded the signal by connecting the radio to the mic input of an HTC EVO 4G smartphone.” And still pulled off the attack with the radio sitting next to the laptop.


 Although I believe there have been some laws made against flying drones in America out of your own field of vision (Darren Kitchen of Hak5 talks about it on Youtube).
Although I believe there have been some laws made against flying drones in America out of your own field of vision (Darren Kitchen of Hak5 talks about it on Youtube).